In a strict secured environment, you may not be allowed perform tasks freely. Only the bastion host (a.k.a jump host) is the one freely allowed to access all systems. In some scenarios restricted environment access is via only through jump host. How will you perform your automation tasks in such scenario?
I was in search for an answer and found a FAQ from Ansible itself. However, scenarios for each people may have different. So, this write is will help you to understand, how to setup properly.
Setup SSH access
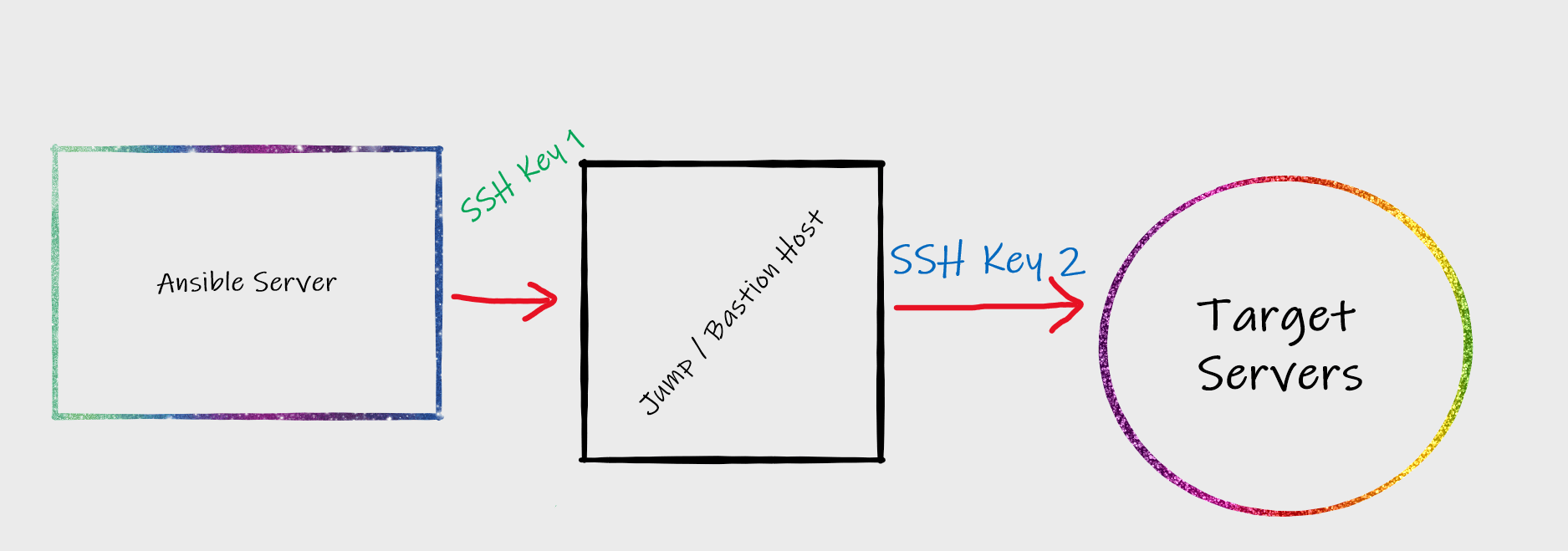
Following is simple illustration about this connection.
As you can see from the diagram, we need to setup 2 different SSH keys first.
- SSH key for connecting from Ansible server to the jump / bastion host. This can be user / root key
- SSH key from jump / bastion host to all target servers. This can also be either user or root key.
Due to security reasons, it is advised to use user key from the jump host to target servers. If you setup root key, any user who can become root user jump host can access these servers and can do anything.
You can also use 2 different users for this purpose. As an example, user1 can be used for SSH from Ansible host to jump host and user2 can be used for connecting from jump host to all target servers.
You must export the private key file ( SSH Key 2) and copy it into safe location in Ansible server.
Configure Ansible
Now you have to configure /etc/ansible/ansible.cfg file enter the path of private key file you copied from jump host
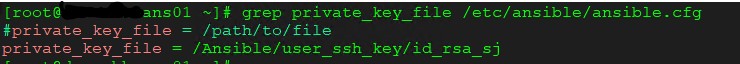
This is all you need to do as a configuration change.
Update Host Variables
You now need to update host variables.
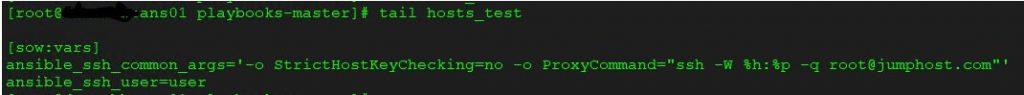
In this section, you have to define 2 variables. First one is ansible_ssh_common_args and second one is ansible_ssh_user. The common argument parameter will define SSH proxy for all hosts defined under that host group. If you want strict host key checking to be enabled, you can remove the line -o StrictHostKeyChecking=no, as shown above. Otherwise you can leave that as it may help if you have any failure with running playbooks.
In this example, I used root user to jump from Ansible host to jump host. So my SSH Key 1 is a root user key.
Now, I have defined a parameter ansible_ssh_user. This will tell Ansible that when you connect from jump host to target servers, use that user. If you don’t define any user here, Ansible will assume that you are running the command as root user. If you want to run as root user, then your SSH Key 2 should be root user key of the jump host.
That’s it. Now you can run a test
Test the Setup
Simply run ansible <host group> -a "command" to test, if the setup is working or not.
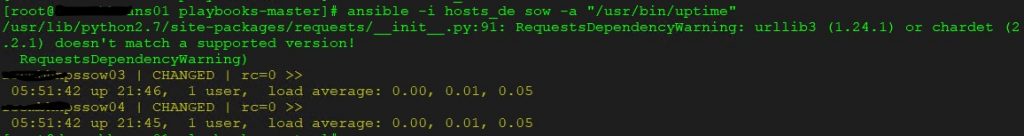
As you can see my test run is successful for the test machines. You can ignore the python related warning as that’s just my local machine issue.
Privileged Execution
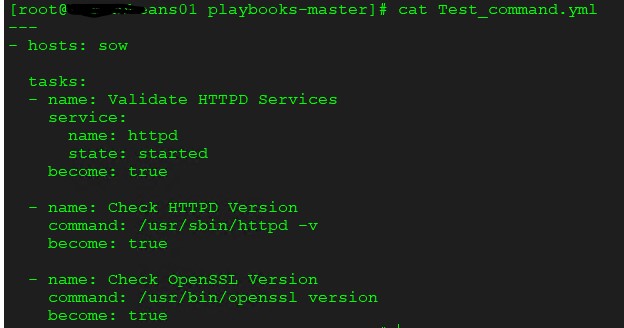
Use become parameter to execute privileged commands, when you run the Ansible playbook with normal user option. A sample playbook shown below for reference.
Disclaimer:
The views expressed and the content shared in all published articles on this website are solely those of the respective authors, and they do not necessarily reflect the views of the author’s employer or the techbeatly platform. We strive to ensure the accuracy and validity of the content published on our website. However, we cannot guarantee the absolute correctness or completeness of the information provided. It is the responsibility of the readers and users of this website to verify the accuracy and appropriateness of any information or opinions expressed within the articles. If you come across any content that you believe to be incorrect or invalid, please contact us immediately so that we can address the issue promptly.
Tags:
Comments
1 Response
Leave a Reply

This article is worthy of recognition and comment. I found this material attention-grabbing and engrossing. This is well-scripted and highly informative. These views appeal to me. This is how real writing is done. Thank you. Visit Us: https://www.ezeelogin.com